Improved Account Security
We have moved to a new sign-in flow for all users as part of one of the DataOps.live recent release. The change improves your account security by enforcing SSO and removing support for passwords for Git over HTTPS.
What this means
New sign-in experience
Users on DataOps.live are directed to a new sign-in experience when logging
in. You will be redirected to auth.dataops.live, which is now the
centralized login service for all of DataOps.live.
Git authentication
Git over HTTPS will no longer support username & password authentication, users must use the more secure Personal Access Token or use Git over SSH instead.
Web IDE and DevReady users are unaffected by git authentication changes.
You can no longer use password authentication when using Git over HTTPS on your local machine. The only supported methods are HTTPS using personal access tokens (PAT) and SSH.
Users who had previously configured username and password authentication must create a personal access token and reconfigure their Git repositories to
username and PAT authentication before running any new git clone, git push,
or git pull commands.
Importing repositories by URL will also be affected by this change, but you can still use this functionality by replacing the password with a personal access token.
SSO login enforced
For customers with SSO configured, SSO logins are now enforced. Users can no longer sign in using username and password.
SSO redirect URL changes
The domain used in redirect URLs is changing from dataops.eu.auth0.com to
auth.dataops.live. Customer SSO configured will need to be updated in advance.
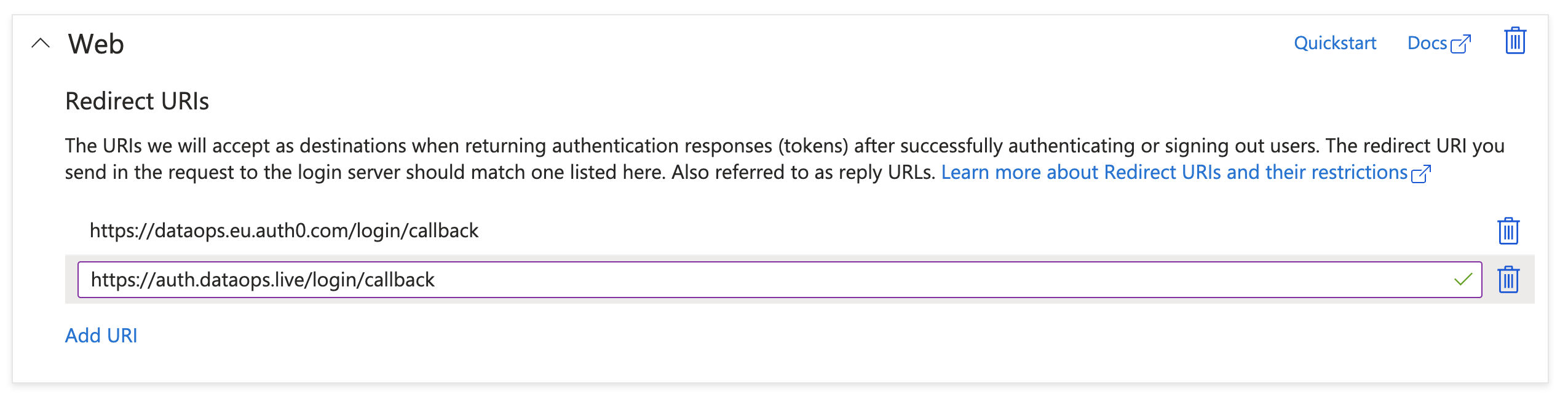
OpenID Connect, Google Workspace & Microsoft Azure AD
OpenID Connect, Google Workspace, and Microsoft Azure AD all support multiple
redirect URLs. Customers simply need to add a new redirect URL from
https://dataops.eu.auth0.com/login/callback to
https://auth.dataops.live/login/callback.
Microsoft Azure AD Example:
Azure -> App Registrations -> DataOps.live -> Authentication
SAML 2.0, ADFS & Ping Federate
Multiple redirect URLs are unsupported for SAML 2.0, ADFS, and Ping Federate. We have worked with customers directly to configure a second connection, which we automatically switched to when the change was rolled out on DataOps.live.
Support for 3rd party email domains
These changes also add support for 3rd party users to be added to your identity provider to allow them to log in to DataOps.live. SSO customers are no longer restricted on the email domains that can be used from their IDP.
Non-SSO customers
For customers not using SSO, users can continue to sign in using their username and password.
Reset/Change password
Non-SSO users can reset/change their password by selecting the Forgot your password? link during the new sign-in experience. Here they can enter their email address and receive a password reset email which will allow them to set a new password for their account.
Getting support
If you have any issues related to the SSO migration, don't hesitate to contact our Support team.