How to Use SSH with Git
DataOps uses the SSH protocol to communicate with Git securely. When you use SSH keys to authenticate to the DataOps.live remote server, you don't need to supply your username and password each time.
Prerequisites
To use SSH to communicate with DataOps, you need:
- the OpenSSH client that comes pre-installed on GNU/Linux, macOS, and Windows 10.
- the SSH version 6.5 or later. Earlier versions used an MD5 signature, which is not secure.
To view the version of SSH installed on your system, run ssh -V.
Supported SSH key types
To communicate with DataOps, you can use the following SSH key types:
- ED25519
- RSA (At least 2048 bits)
Checking for existing SSH key pair
Before you generate a key pair, see if a key pair already exists.
-
Go to your home directory's
.ssh/subdirectory. -
See if a file with one of the following formats exists:
Algorithm Public key Private key ED25519 id_ed25519.pubid_ed25519RSA id_rsa.pubid_rsa
Generating the SSH key
If you do not have an existing SSH key pair, generate a new one:
-
Open a terminal.
-
Run
ssh-keygen -tfollowed by the key type and an optional comment. This comment is included in the.pubfile that's created. Use your email address for the comment.For ED25519:
ssh-keygen -t ed25519 -C "your.email@example.com"If you are using a legacy system that doesn't support the ED25519 algorithm, use 4096-bit RSA:
ssh-keygen -t rsa -b 4096 -C "your.email@example.com" -
Press Enter. Output similar to the following is displayed:
Generating public/private ed25519 key pair.
Enter file in which to save the key (/home/user/.ssh/id_ed25519): -
Accept the suggested filename and directory unless you want to save it in a specific directory where you store other keys.
-
Specify a passphrase:
Enter passphrase (empty for no passphrase):
Enter same passphrase again:A confirmation is displayed, including information about where your files are stored.
A public and private key are generated. Add the public SSH key to your DataOps account and keep the private key secure.
Adding the public SSH key to your account
-
Copy the contents of your public key file. You can do this manually or use a script. For example, to copy an ED25519 key to the clipboard:
macOS
tr -d '\n' < ~/.ssh/id_ed25519.pub | pbcopyLinux (requires the
xclippackage)xclip -sel clip < ~/.ssh/id_ed25519.pubGit Bash on Windows
cat ~/.ssh/id_ed25519.pub | clipReplace
id_ed25519.pubwith your filename. For example, useid_rsa.pubfor RSA. -
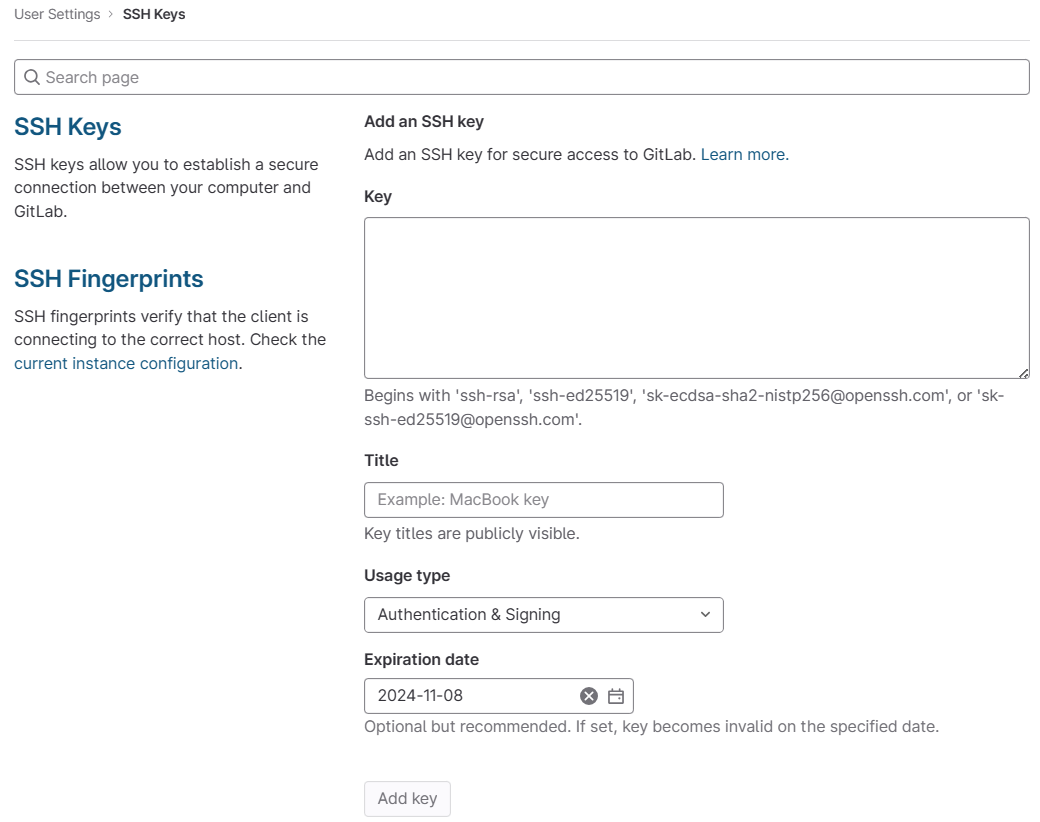
Go to User Settings > SSH Keys
-
In the Key box, paste the contents of your public key. If you manually copied the key, make sure you copy the entire key, which starts with
ssh-rsaorssh-ed25519, and may end with a comment. -
In the Title box, type a description, like
Work LaptoporHome Workstation. -
Optional. In the Expires at box, select an expiration date. In:
- DataOps checks all SSH keys at 02:00 AM UTC every day. It emails an expiration notice for all SSH keys that expire on the current date.
- DataOps checks all SSH keys at 01:00 AM UTC every day. It emails an expiration notice for all SSH keys that are scheduled to expire seven days from now.
-
Select Add key.
Git clone
-
Perform your
git cloneoperation now as follows:git clone git://app.dataops.live/group/project.git -
If this is the first time you connect, you should verify the authenticity of the DataOps host. If you see a message like:
The authenticity of host 'app.dataops.live (35.178.252.56)' can't be established.
ED25519 key fingerprint is SHA256:ao2qAUiobpGcK4uAdt3yHdSnHlInmpaV85/7K+sLHwM.
This key is not known by any other names
Are you sure you want to continue connecting (yes/no/[fingerprint])?Type
yesand press Enter.
Caching your private key for the session
If you have set a passphrase from your SSH key, it quickly becomes inconvenient to have to enter it with every Git command.
To safely cache the private key for your session, execute the following two commands in your shell:
eval "$(ssh-agent)"
ssh-add
Subsequent git commands won't prompt you for the passphrase again.